Gain 10x visibility of critical risks with deep insight of cloud exposures.
Get a 15 minute demo
Experience Hadrian
Hadrian’s end-to-end offensive security platform sets up in minutes, operates autonomously, and provides easy-to-action insights.





Cloud infrastructure can evolve rapidly leaving security teams in the dark and unaware of issues. Hadrian connects to multiple cloud environments with a few clicks, providing a centralized view of exposed assets. New cloud assets and changes are detected in real time, with visibility tailored for fast team responses.
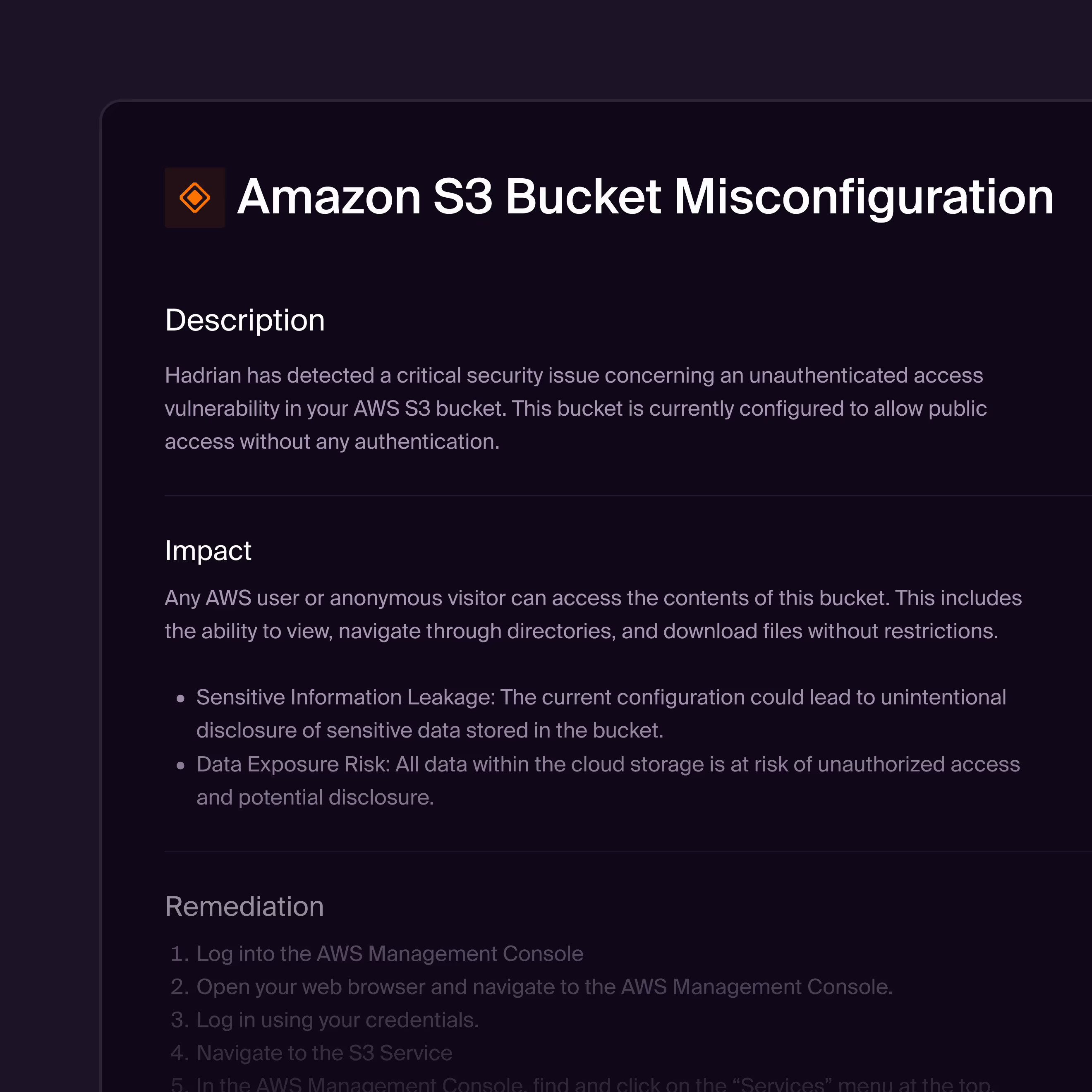
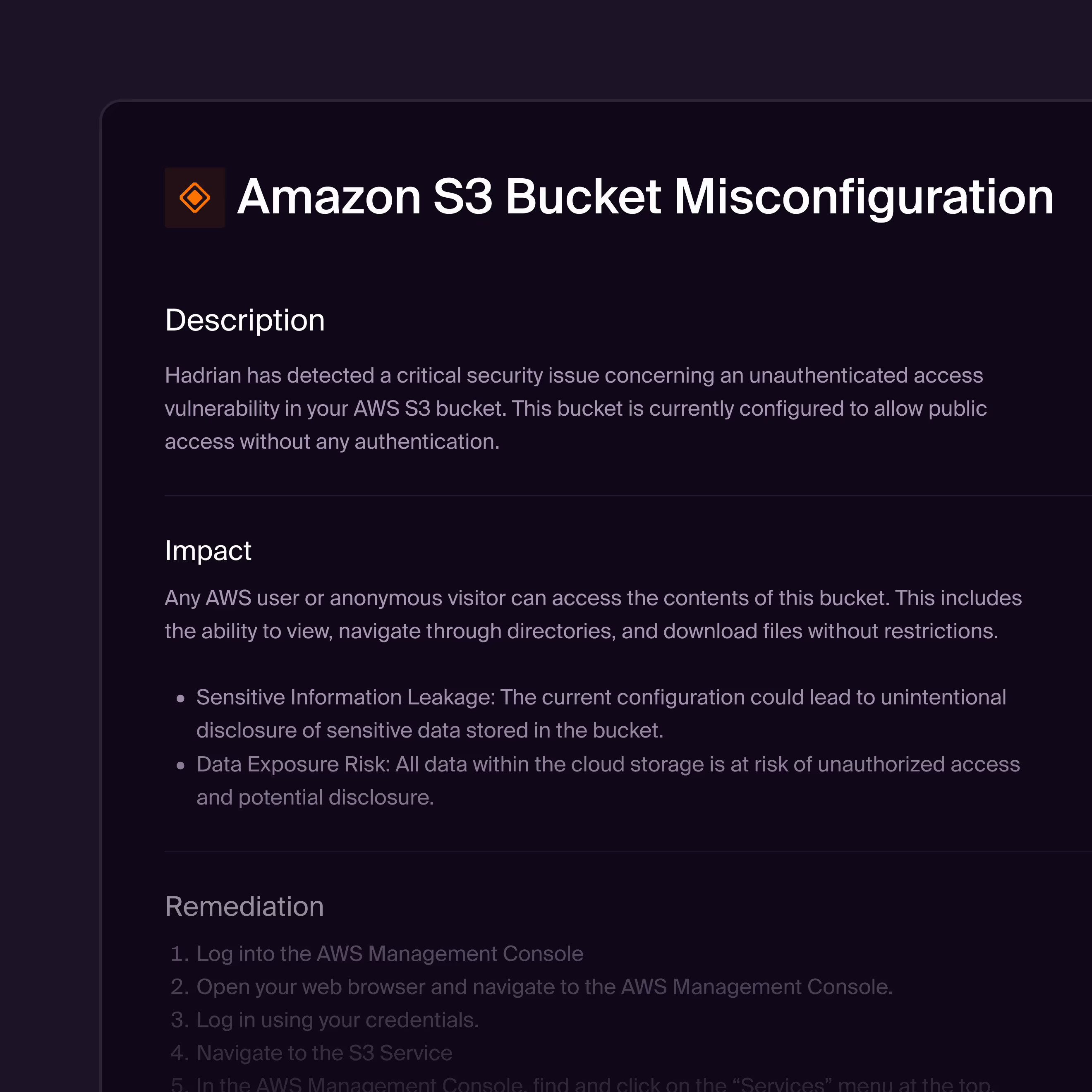
Cloud infrastructure is a prime target for hackers due to the ease of lateral movement once access is gained. Hadrian identifies exposed cloud assets and misconfigurations that could enable lateral movement and privilege escalation. Hadrian’s Orchestrator AI verifies exploitable risks, helping teams focus on the most impactful issues.
A slow response can turn a minor issue into a major breach. Hadrian’s ML algorithms prioritize risks based on business relevance, asset attractiveness, discoverability, impact, and exploitation ease. Security teams can easily track the frequency of cloud exposures and remediation speed with built-in reporting.


%201.png)





%201.png)















%201.png)





%201.png)













Hadrian is an agentic AI offensive security platform that helps modern security teams prevent breaches before they begin. Agentic AI continuously discovers internet-facing assets, emulates attacker behavior, and validates which exposures are truly exploitable—cutting through noise and prioritizing what matters most. Hadrian delivers 10x visibility into critical risks, eliminates 99.4% of alert noise with reliable validation, and reduces remediation time by 80% with clear, reproduction-ready guidance.
Traditional scanners rely on static lists of known vulnerabilities (CVEs) and often produce a high volume of false positives. Hadrian goes beyond simple detection by performing Adversarial Exposure Validation. Our platform safely simulates real-world attack techniques to validate if a vulnerability is actually exploitable in your specific environment. This means we don't just tell you something might be wrong; we prove whether it matters.
We solve alert fatigue through validation. Most security tools flood teams with alerts based on theoretical severity (CVSS scores). Hadrian filters this noise by attempting to exploit the finding. If a vulnerability cannot be exploited due to a firewall or configuration, we deprioritize it. We only flag verified risks (true positives) that have a confirmed path to compromise, allowing your team to focus on what actually needs fixing.
Yes. One of our primary capabilities is autonomous asset discovery. We continuously scan the internet to find forgotten subdomains, cloud instances, and legacy servers that belong to your organization but aren't in your official inventory. You can’t protect what you can’t see, and Hadrian ensures you have 100% visibility over your external perimeter.
Get a 15 minute demo
Hadrian’s end-to-end offensive security platform sets up in minutes, operates autonomously, and provides easy-to-action insights.