Gain 10x visibility of critical risks that could result in downstream attacks and brand damage.
Get a 15 minute demo
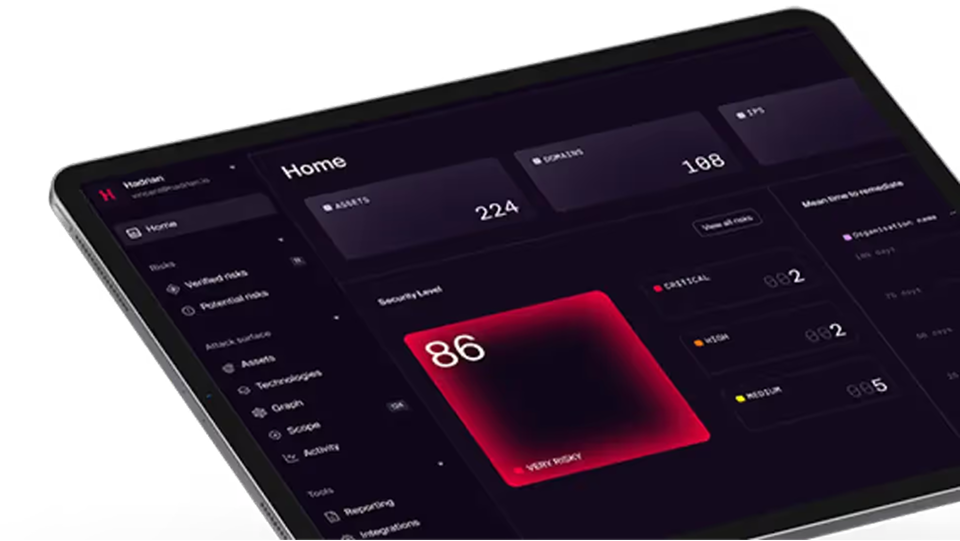
Experience Hadrian
Hadrian’s end-to-end offensive security platform sets up in minutes, operates autonomously, and provides easy-to-action insights.








%201.png)





%201.png)















.png)
.png)