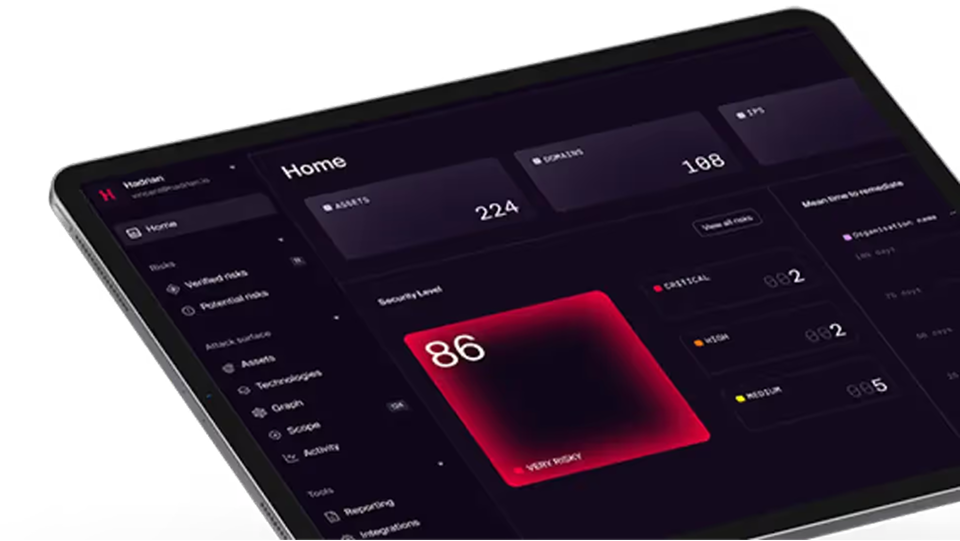
Discover and contextualize your attack surface continuously. So you have 24/7 oversight of 100% of your internet facing assets.
Get a 15 minute demo
Experience Hadrian
Hadrian’s end-to-end offensive security platform sets up in minutes, operates autonomously, and provides easy-to-action insights.









%201.png)





%201.png)















.png)
.png)